What is blockchain
First things first, a brief explanation of what the blockchain is:
- Blockchain is the underlying technology behind Bitcoin and other cryptocurrencies.
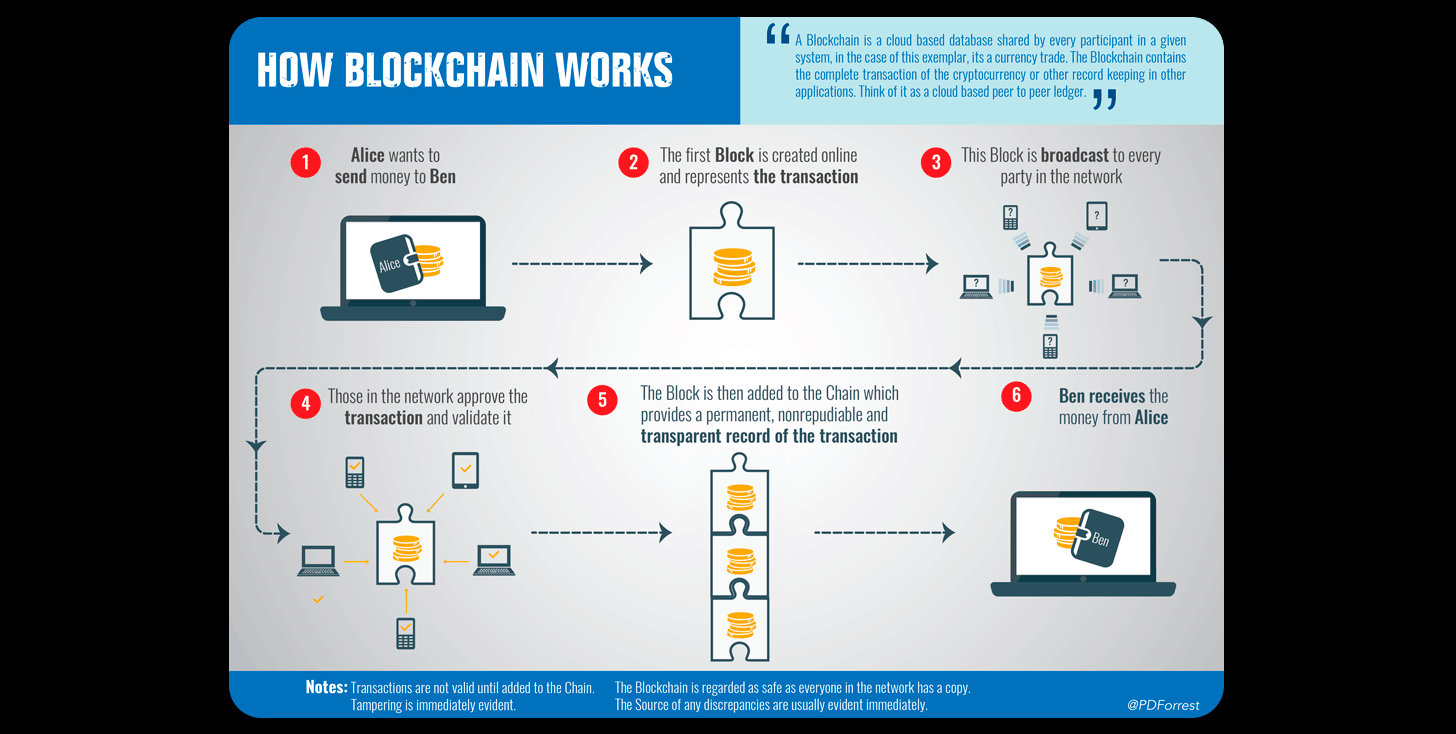
- The blockchain is a digital ledger (think a spreadsheet) distributed on an open peer to peer network. Think a banks ledger they use to write and keep a record of their customers transactions and any related information of that transaction. On a cryptographic blockchain (any cryptocurrencies native blockchain) all information about that transaction is encrypted using cryptography. See encryption and cryptography in the glossary.
- A blockchain is not a Bitcoin and a Bitcoin is not a blockchain. Bitcoin is a type of cryptocurrency while the blockchain is a certain type of innovative technology.
- Anyone with a computer can view and/or verify every transaction on the blockchain. Every transaction that's ever taken place on the network, and every transaction that will ever occur will be recorded on the blockchain.
Imagine for a second, a imaginary chain with blocks. For every one foot of digital chain, there is a digital block. Within these blocks are information that can range from transaction histories to any form of record keeping. This information is stored in a chronological order. If something needs modification in any way, instead of going back and editing previous information, another block is created with the new information embedded in it, leaving the old transaction in previous blocks and new transactions in the new blocks. Even though the information on the previous block may be old, the information within it is never altered. Before blockchain, recorded ledgers of information would be kept on a central system of some sort (a notebook, Excel, etc.).
Why blockchain?
One of the primary features of blockchains are their security. Blockchain networks are decentralized, meaning that their “ledger” is spread out across thousands of computers, or “nodes,” as peer-to-peer networks. These nodes independently validate the information entered on the blockchain, which greatly reduces the ability to alter the digital ledgers in any way. If everyone has the same information on their computer, and can verify the transactions that take place on it, a transaction that does not belong (i.e. hacking) can be seen and rejected.
Here’s an example of how a blockchain prevents a hacker from altering a transaction:
We have three people in this scenario: Person A,Dustin, Person Z, Alika, and Person H, Keone. The rest of the letters in the alphabet will represent every other node on the network.
Person A, Dustin, sends funds to Person Z, Alika, on a blockchain. When Dustin (A) sends something to Alika (Z), it is broadcasted to all of the nodes (computers) on the blockchain (person's B,C,D,E,F,G,H,I,J,K,L,M,N,O,P,Q,R,S,T,U,V,W,X,Y), which by the way is also secured by a cryptographic identity (or public keys). Let’s say that Person H, Keone, is a hacker. He sees this transaction between Dustin (A) and Alika (Z) and wants to alter it in his favor so that it appears that Dustin (A) sent the transaction to him (H) instead. The difficulty in this is that if Keone (H) wanted to change something about that transaction, he would somehow have to prove to the 23 other nodes (computers) individually and that he is in fact the recipient of that transaction. Remember, everyone on the blockchain can see and more importantly, verify every transaction becausethey all start with the same information. The same digital ledger. This presents a big problem for Keone the hacker in that he would have to expend massive amounts of time energy and resources. In the blockchain world, the energy and resources normally are accompanied by large price tags. Basically, for hackers, the downsides far outweigh the benefits. For users of that blockchain however, it provides a secure system of trust in which they can openly transact with each other.
Note: Within a traditional payment system, we use third-parties (banks, brokers, etc.) to verify our day-to-day transactions. Within a blockchain though, the network serves as the validating authority. This lack of reliance on a central entity is what makes blockchains "decentralized." And within this system, users are able to securely transact with each other without the need of a third-party.
Lets review:
- Blockchains are digital ledgers on which information is stored. This information is immutable, which means it cannot be altered once it is recorded and verified.
- The information on these blockchains are broadcasted to hundred of thousands of individual nodes (computers) on the network. These nodes verify this information, which add to the security of the blockchain. If an individual wanted to hack into the blockchain he would have to attack all of these nodes simultaneously.
- The use of these multiple nodes reduce the need for a central entity to verify the information. This gives blockchain its unique decentralized ability.
Here's a simplified video on blockchain:
For a more in depth breakdown to the inner workings of cryptocurrencies, and just what it means to "own" a cryptocurrency like Bitcoin, check out this video made by our friends at 3Blue1Brown.